Assigning risk levels for each employee in your organization can be tricky. The highest risk users and lowest risk users may be obvious, but what about all those users in between? You can't necessarily group them all together. How do you make that decision for each user?
Identity Automation Blog
Blog Categories
- Cybersecurity (134)
- Company News (101)
- K-12 Education (80)
- RapidIdentity (71)
- Multi-Factor Authentication (69)
- Higher Education (44)
- Identity Governance (43)
- Identity Lifecycle Management (32)
- Single Sign-On (32)
- Healthcare (29)
- Access Management (19)
- Government & Public Sector (5)
- Identity Automation Pathfinder (1)
Recent Posts by Josh Orum
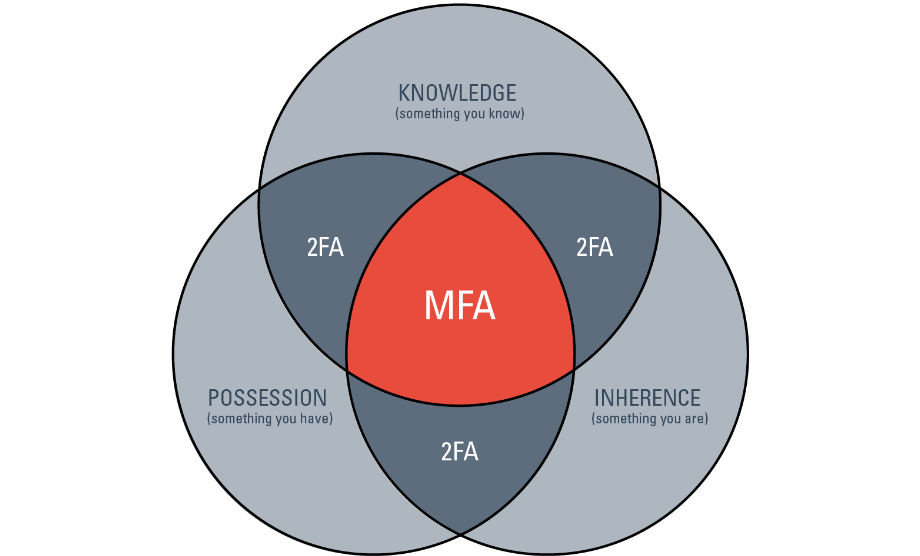
What is Multi-Factor Authentication?
Yesterday we announced RapidIdentity 3.5 and unveiled our vision for multi-factor authentication.
Today we thought we'd provide a little refresher on the basics of MFA and its benefits. Check out the graphic below to learn more.
Meeting the Challenge of Identity Automation in Schools
The new school year has begun and so have the challenges that come with managing thousands of student accounts. Recently, we saw an article about one school district in Tennessee that experienced the chaos of manual identity management first hand when they attempted to deploy their iPads for Kids Program.
How to Integrate Cloud Applications with Dedicated Utility Accounts
With all the cloud products and applications now available, more organizations are finding it valuable to integrate them, such as linking Salesforce.com to your accounting package so data from both can be viewed together. However, as companies integrate cloud accounts, we’ve noticed a number of them run into problems maintaining those integrations down the road. When integrating cloud accounts, you often need to choose an internal user account to create the bi-directional connections and truly link the applications. For example, if we were to connect Hubspot to Salesforce, we would need to enter a Salesforce account (username and password) into Hubspot. This process works fine until the person who owned that Salesforce account leaves the company. When that happens, the integration you previously had is now useless.
Analyzing and Improving Student Privacy in Education
Privacy in education is a subject that has received significant attention recently, and we see it garnering even more attention in the future. It affects students, teachers, administrators, parents, IT staff and IT vendors. All involved tread a fine line, balancing the security issues that are vital to the operation of a school with the individual privacy rights of the actual classroom users of technology.
Learn the Benefits of Automated Identity Access Management
Did you know that 50-60% of today’s organizations still rely on manual Identity Access Management (IAM)?
While automated IAM technologies like RapidIdentity enable administrators to automatically provision and monitor users and grant time-based access, manual IAM requires admins to manually change these factors for each individual within the organization. This system can lead to lapses in access restriction and ultimately large losses in time, money and security.
Are You Ready to Contain the Inevitable?
You can take all the security precautions in the world, but if someone really wants to attack your organization’s infrastructure, they’re going to find a way. With hackers who are able to stay one step ahead of the security precautions we put in place, it’s not inaccurate to say that it’s inevitable you will be attacked.
Your Biggest Security Threat? Rogue Employees
Guess who may be bringing unwanted risk to your organization? Surprisingly, it’s a rogue employee. Even Oracle CEO, Mark Hurd, had this to say: “Most cyber attacks are not from nation states. Most, like 95 percent, come from within a company’s four walls.”
But do you know how to spot them? And how you can stop them?
Many of the biggest attacks originate from inside the enterprise from fully authenticated users. And these rogue employees don’t always have malicious intent; sometimes they’re dedicated employees who mistakenly committed an oversight.
Is Your School District Ready for an IT Advisory Committee?
Peek inside any K-12 classroom and you may find students taking a test on a desktop computer or a teacher connecting with a satellite school via video conferencing. Technology has transformed the regular classrooms of today to the learning centers of tomorrow.
RapidIdentity: Renaming our Products
Today, I’m writing with a big announcement. When we introduced our new brand identity several months ago – a new logo, new website, and new marketing materials – we were changing our look to better represent who we are today, and who we’ll be tomorrow – a provider of world-class identity management solutions.
current_page_num+2: 3 - disabled