A white paper released by PIXM highlights an alarming trend in cyberattacks targeting school districts across the United States. This document uncovers a significant uptick in spear phishing campaigns over the last two months, orchestrated by two notorious threat groups known as Tycoon and Storm-1575.
Identity Automation Blog
Blog Categories
- Cybersecurity (134)
- Company News (101)
- K-12 Education (80)
- RapidIdentity (71)
- Multi-Factor Authentication (69)
- Higher Education (44)
- Identity Governance (43)
- Identity Lifecycle Management (32)
- Single Sign-On (32)
- Healthcare (29)
- Access Management (19)
- Government & Public Sector (5)
- Identity Automation Pathfinder (1)
Enhancing Security with OAuth 2.1: What You Need to Know
OAuth is a standard for sharing user account authentication data across various platforms. The name of this technology is quite literal - it's called Open Authorization. OAuth is an open standard that has been in development since 2006 when software engineer Blaine Cook worked on Twitter's OpenID implementation. Google joined in 2007, and OAuth 1.0 was released in 2010. Since then, many tech companies, including Facebook (Meta) and Microsoft, as well as smaller platforms, have adopted the open standard. OAuth 2.0 was published in 2012 and has been the most widely used open standard for user account federation ever since.
Passwordless Authentication
Passwords are one of the most confusing concepts in secure authentication for typical users.
What is ITDR (Identity Threat Detection Response)
The past couple of decades have seen an immense evolution in the cyber threat landscape and how organizations and enterprises utilize IT. Threat actors develop new cyber exploitation techniques, and concurrently cybersecurity solution vendors develop new technologies and methodologies. Those new technologies and methodologies often get branded with a new acronym that soon became part of the vernacular of SOC analysts everywhere.
QR Codes are an Emerging Cyberattack Vector
It’s 2023, and QR codes have been ubiquitous for well over a decade now.
Protecting Your Institution from the Threat of Spear Phishing
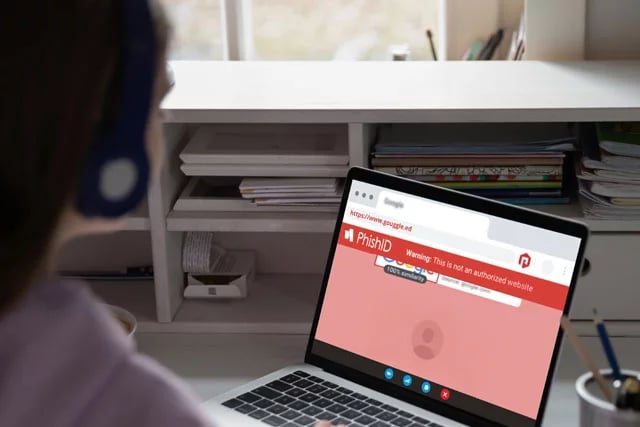
Spear phishing is one of the most potentially destructive types of cyberattacks ever.
Next-Generation Identity and Access Management: Empowering Your State's Education System with a Universal Identity Fabric
In the realm of education, where data drives innovation in student outcomes, security is paramount. Unfortunately, coordination and collaboration at state and local levels has been cumbersome and complex, which slows down improvements in both cybersecurity and student outcome innovation. It's time for a different approach to identity management among state education systems with identity and access management that overcomes the challenges of coordination and collaboration across districts, agencies and higher education institutions.
The Evolution of Technology and the Power of IAM
.png?width=900&height=235&name=ISTE%20header%20(1).png)
Sumner-Bonney Lake School District Spotlight: Why RapidIdentity is a "Game Changer" for K-12
Spanning across the cities of Sumner and Bonney Lake, Washington, Sumner-Bonney Lake School District supports 1,075 employees and a steadily climbing student body of 10,000 through its identity access management (IAM) system management (IAM) system.
Identity Automation’s 2023 FETC Conference Recap
The 2023 FETC Conference in New Orleans just wrapped up, and our entire on-the-ground Identity Automation team was humbled to accept one of the industry’s top honors in the industry while also hosting a packed happy hour event, demonstrating award-winning IAM solutions, and meeting with top thought leaders throughout the four-day event.
current_page_num+2: 3 -