Today we announced RapidIdentity 3.5, the latest generation of our identity and access management solution. In making that announcement, we’re also revealing our vision for multi-factor authentication.
Authentication is an important security technology. It’s an organization’s first line of defense against attacks. Not having user authentication in place is equivalent to leaving the front door to your house unlocked. Lack of authentication is like rolling out a red carpet for cyber criminals.
However, using one authentication method with all employees is not enough to provide the level of security you need in all cases.
Many organizations utilize a username/password approach to authentication, but passwords, even strong ones, can be susceptible to phishing, reverse engineering and brute force attacks. Challenge responses, those questions that you’re asked like the street you grew up on or your mother’s maiden name, can be guessed - sometimes fairly easily with the help of social media. Even biometric data, made popular with consumers through the fingerprint scans on smartphones, can be copied fairly easily from physical contact or digital copying. Even worse with biometric data is that if that piece of data is stolen, you can never change it. If a password is stolen it can be reset, but you can’t reset your fingerprint.
Over the past several years, we’ve developed a vision for what multi-factor authentication should be, supported by four pillars, and we based RapidIdentity 3.5 on that vision. The solution encompasses our secure vision for the industry and is a solution that we believe will help organizations move away from their dependence on passwords to a secure, flexible multi-factor authentication environment.
Identity Automation Multi-factor Authentication Vision
- Multi-factor authentication is now necessary to properly secure organizations.
Multi-factor authentication (MFA) is a necessary step up from two-factor authentication , which many IAM vendors tout. Two-factor authentication simply requires a user to provide two forms of authentication, such as a password and the correct response to a challenge question.
With MFA, a user may be required to provide:
- Something they know (knowledge)
- Something they have (possession)
- Something they are (inherence)
There are a number of different authentication methods that can be used to meet these three criteria, which I’ll actually touch on later in this post, but you can see that the MFA requirement is much stronger and more difficult to compromise than two-factor authentication.
You may not want to require MFA authentication of each and every user, but you need it for those users who carry more risk. So a vendor touting its two-factor authentication system to apply to all employees is not providing you with the most secure authentication for your organization as a whole.
- Different Users Require Different Authentication Methods
Why are passwords used so commonly as an authentication method? Are they an appropriate method for every single user you manage? Probably not, but many organizations are locked into a password-dominated authentication process due to legacy security frameworks. That’s why we juggle so many passwords now. It sets us up for a reality where users utilize simple, easy to remember (and also easy to crack) passwords, leading many to become rogue employees. Not the most secure approach.
We don’t have to be so dependent on passwords. We believe you should offer a number of different authentication methods for your employees because every employee is different. Here’s what we now offer - a variety of options that fit into those Something You Know, Something You Have and Something You Are buckets I mentioned earlier.
|
Something You Know (Knowledge) |
Something You Have (Possession) |
Something You Are (Inherence) |
| Password | SMS One-time Password | Fingerprint Scan |
| Challenge Response | Smart Card | Facial Recognition |
| Pictograph | Geolocation | |
| Kerberos Credentials | Bluetooth Proximity | |
| Social Media Credentials | RFID | |
| Magnetic Strip Card |
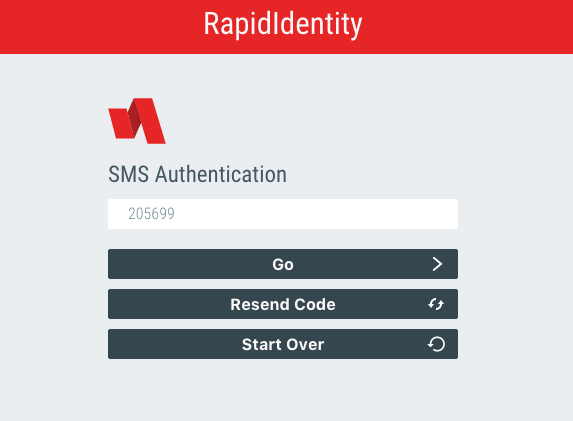 RapidIdentity 3.5 login screen using SMS One-time Password as an authentication method
RapidIdentity 3.5 login screen using SMS One-time Password as an authentication method
- Policy-driven Authentication is a Must
Now we get into the more technical side of authentication that enables organizations to implement MFA and offer users different authentication methods. Not all users are the same and policy-driven authentication allows organizations to easily personalize authentication methods based on a user’s specific circumstances.
A multi-factor authentication approach should enable policies to be created and enforced based on attributes, roles, entitlements and/or risk scoring. This makes the authentication process customized by user, but without the increased time and resources usually associated with the word ‘custom’. Additionally, MFA should allow for its policies to be adaptive because one user carries different risk levels in different situations. Are they inside or outside the corporate network? Is it 11am when they’re normally working or is it 11pm when they’re rarely, if ever, online? Is it a Tuesday or a Saturday? All of those scenarios carry very different risk levels, and your MFA needs to be able to adapt to those by user.
If an organization doesn’t utilize policy-driven authentication, the organization simply isn’t secure enough.
RapidIdentity 3.5 is the first policy-driven adaptive, multi-factor authentication.
- Modular Architecture is Necessary for Scalable, Flexible Multi-factor Authentication
As we move further and further away from a dependence on passwords, new authentication methods will continue to be introduced. Yet many organizations have authentication methods that are so deeply ingrained in their system that they’re unable to quickly add new methods. They’re stuck with what they have. A modular, plug-and-play authentication architecture enables organizations to rapidly add new authentication methods without affecting policies already in place. This is very necessary in order to continue adapting to the risks organizations face and changes in user behavior.
We believe this vision for multi-factor authentication is what the industry must move toward in order to best secure all organizations. A ‘one size fits all’ approach no longer works. Different risk levels require different authentication policies and multi-factor authentication accommodates that. To learn more about RapidIdentity 3.5 and how it’s fulfilling this vision of multi-factor authentication, contact us to schedule a conversation.

Comments