
The K12 world has been given a call to action. With no time to prepare, no playbooks to reference, and the very core of their mandate being challenged, school districts are now faced with the prospect of reshaping their entire educational delivery system overnight.
Now that schools across the country are shut down to limit the spread of COVID-19, every morning for the foreseeable future, students will log in remotely for lessons with their parents acting as substitute teachers and their kitchens and dining rooms as makeshift classrooms.
How do we teach in this new world? How do we deliver strong educational outcomes when we no longer have the four walls to provide instruction within?
Schools have taken off with a shot. Lesson plans have been re-built and re-purposed. New technologies have been rolled out at breakneck speed. Necessity is driving innovation and reshaping the daily lives of students, teachers, and administrators.
But innovation can be messy. In this rush to adapt, we’ve struggled to incorporate sensible controls to mitigate our data and our systems from risk, but there have been major stumbles along the way from which we can learn. The most notable example being the recent attention around Zoom meetings and the practice of “Zoombombing,” the intrusion of uninvited participants into video meetings in which they’ll either passively listen or actively hijack the meeting and harass participants.
Due to this growing trend, Zoom has been prominently featured in the news lately for its perceived lack of privacy and security standards. Beyond this, state and federal government officials have announced Zoombombing could lead to state or federal charges and the FBI has even gotten involved by issuing a warning regarding these Zoombombing incidents.
All of this has culminated in school districts are starting to pull away from the application with The New York City Department of Education being the first major player to ban Zoom from being used in their schools.
But is Zoom really as dangerous as they are saying? We don’t think so.
HOW You Use Video Conferencing Matters
In a lot of cases, and certainly in this case here, it is not necessarily the application which causes issues, but how you are using it. Zoom is enterprise software created for business applications, not schools. So bringing this software into a K12 environment means making adjustments to how students and teachers approach it. By using any application or platform without the proper controls in place, even a secure platform can quickly become insecure.
For schools questioning how to move forward with Zoom or any video conferencing platform, there are two major controls we recommend districts leverage: Operational Policy and Logical Policy.
Operational Policy means providing users with guidance on how to use new tools in a secure way. For example, much of the challenge hitting the K12 world today around Zoom is due to poor usage guidelines. Schools have been making their meetings public, rather than by invitation. Meetings are not password protected. Sharing rights are not locked down.
This is similar to a teacher instructing their class to use an application that the teacher finds useful, but has not taken through proper Operational Policy. In their desire to bring value to the classroom, they may be uploading sensitive student information into services that may not have secure policies on the governance of the data, or at worse, may itself be a malicious tool.
Here is an example of a simple operational policy regarding the use of Zoom or any other video conferencing:
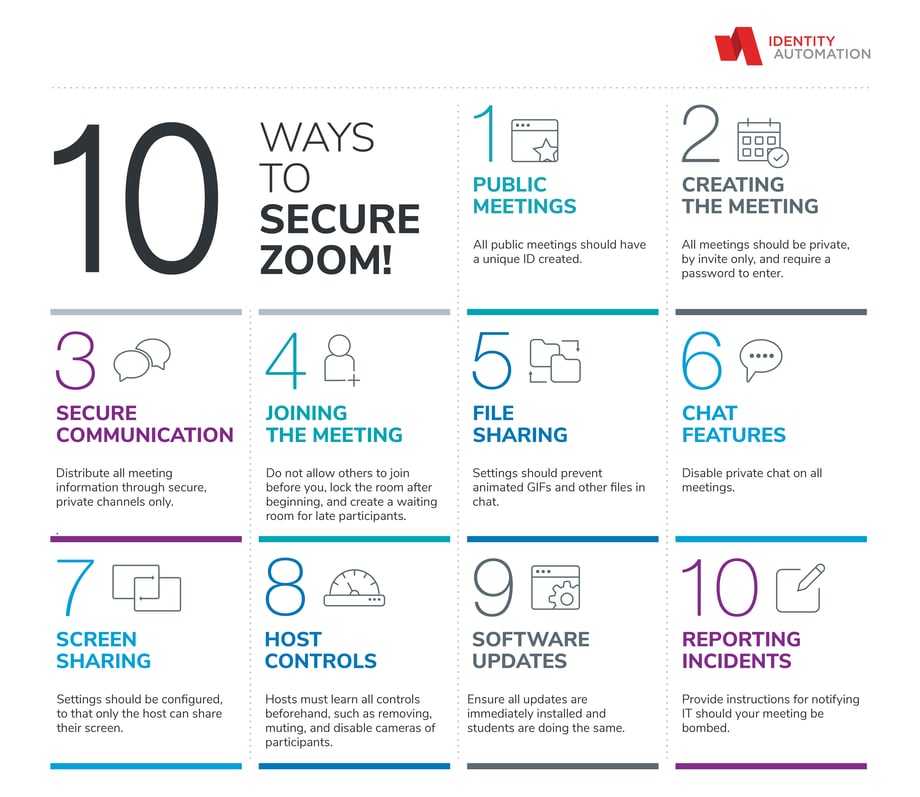
With policies such as these in place, the chances of your student privacy and network security being compromised is dramatically reduced.
Creating A Security Foundation for A Better User Experience
The second control we recommend is a Logical Policy, which should be part of a larger, comprehensive Identity and Access Governance Strategy. Logical Policies govern who has access to what resources and under what circumstances they are able to access that resource.
Logical Policies are used to protect sensitive data, or protect the identities of your users. They manifest in critical areas, such as Multi-Factor Authentication, Zero or Least Privilege, and Risk-Based Access Controls.
For example, a good Logical Policy would be allowing only teachers access to sensitive student data or allowing only IT administrators to control what applications to which users have access. Alternatively, we’d recommend against policies that provide no control, such as allowing teachers to determine all applications for their class and provide that data to the application directly.
So, what are the ways school districts can create a good security foundation to move toward a better end user experience? By utilizing Single Sign-On, Access Controls, and strong Authentication.
Single Sign-On ensures teachers and students get secure, streamlined access in one place, with one password. In addition, by having access policies in place that enforce a Zero Trust Model, you’re limiting the risk your district is taking on.
During this COVID-19 lockdown, a good access control for schools to put in place would be limiting user access to resources based on geographical locations, meaning a user cannot log into district applications from China, as it is highly unlikely a student is attempting to complete their lessons from a different country—a good risk-based authentication criteria.
Beyond consolidating and limiting access, you also want to lock it down with stronger authentication—and authentication tailored for students in particular. Because of the ease of implementation needed during this epidemic shut down, we recommend pictograph authentication, which allows users to select the images that comprise their password and pairing with a username and password for older students.
Adding these safeguards onto your security strategy creates a strong foundation for the future. If you imagine your Logical Policy like this, enforced and managed by an Enterprise Identity and Access Governance Solution, as the hub of a wheel, it makes solid, and governs the spokes that comprise your digital resources. Adding new systems or resources allows them to “spoke” into the hub, and gird the whole of your enterprise security strategy.
The Shut Down and Beyond
With the end of the school year taking a much different turn than any of us expected, school districts, teachers, administrators, students, and parents have been coming together to make education work in a new way during these uncertain times.
With no playbook to read from, the switch from in-person to 100% online learning has been impressive, but challenging. In the coming days, schools will need to use applications and resources in ways they never have before to accommodate these new circumstances. Our recommendation across the board is to remember that utilizing good Operational and Logical Policies is half the battle.
Furthermore, creating a foundation of security and governance will make adding new applications and resources a streamlined process now, and years into the future, which will serve your district not only during this crisis, but beyond it as well.

Comments