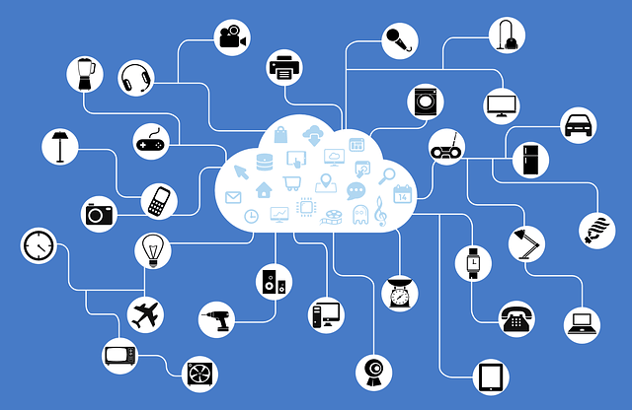
To say that the Internet of Things (IoT) has been a hot topic lately would be an understatement. Over the last few years, talk about IoT has rocketed from zero to a hundred, and has created a growing number of eager early adopters who want to take shiny, new IoT devices home with them right now. At the same time, some businesses have already started dipping their toes into the IoT lake. However, like many technologies ahead of their time, the increase in the number of IoT devices is quickly outpaced by the number of ways they can be breached by cyber criminals.
The cracks in the early infrastructure of the Internet of Things are already beginning to show. Most recently, reports have uncovered that even the most non-threatening of items, specifically internet-connected baby monitors, have a surprisingly large potential for breaches. While the intent of the device is to allow parents to check in on their young children through the internet from anywhere in the world, it also can allow malicious hackers to do the same. Examples like this make it clear that with unsecured IoT in every threshold of your home, having a creep watch your youngsters sleep from across the globe may be just the beginning of the dangers of IoT devices.
For businesses, rampant unsecured IoT devices can spell just as much bad news as at-home IoT devices. With millions or billions of dollars at stake, a data breach in a single IoT device can cause an organization’s potential for liability to skyrocket. According to an article this year in the Boston Globe, most companies who come to understand the potential threat of IoT devices are “scared, aware, but not sure what to do”.
At present, options to secure devices in the Internet of Things may seem few and far between. However, the future may hold some creative, successful ideas for managing the Pandora’s box of security issues that internet-enabled devices will have. Perhaps by using the next generation of today’s multi-factor authentication technologies, your smart coffee pot will be able to tell that it’s you based on time of brewing and coffee roast.
Identity management technologies, after all, are how many enterprise systems are currently secured. It’s also the layer of security currently applied to you by many of the internet services you use today such as Facebook, Gmail and Dropbox. Is it that much of a stretch to think that your car or your house’s heating and cooling or your refrigerator may require some type of user authentication?
While the bright future of IoT devices may seem tainted at present by the security threats they currently possess, the future holds the promise of devices that not only add a new dimension to our lives - but also can keep our most critical information secure.

Comments