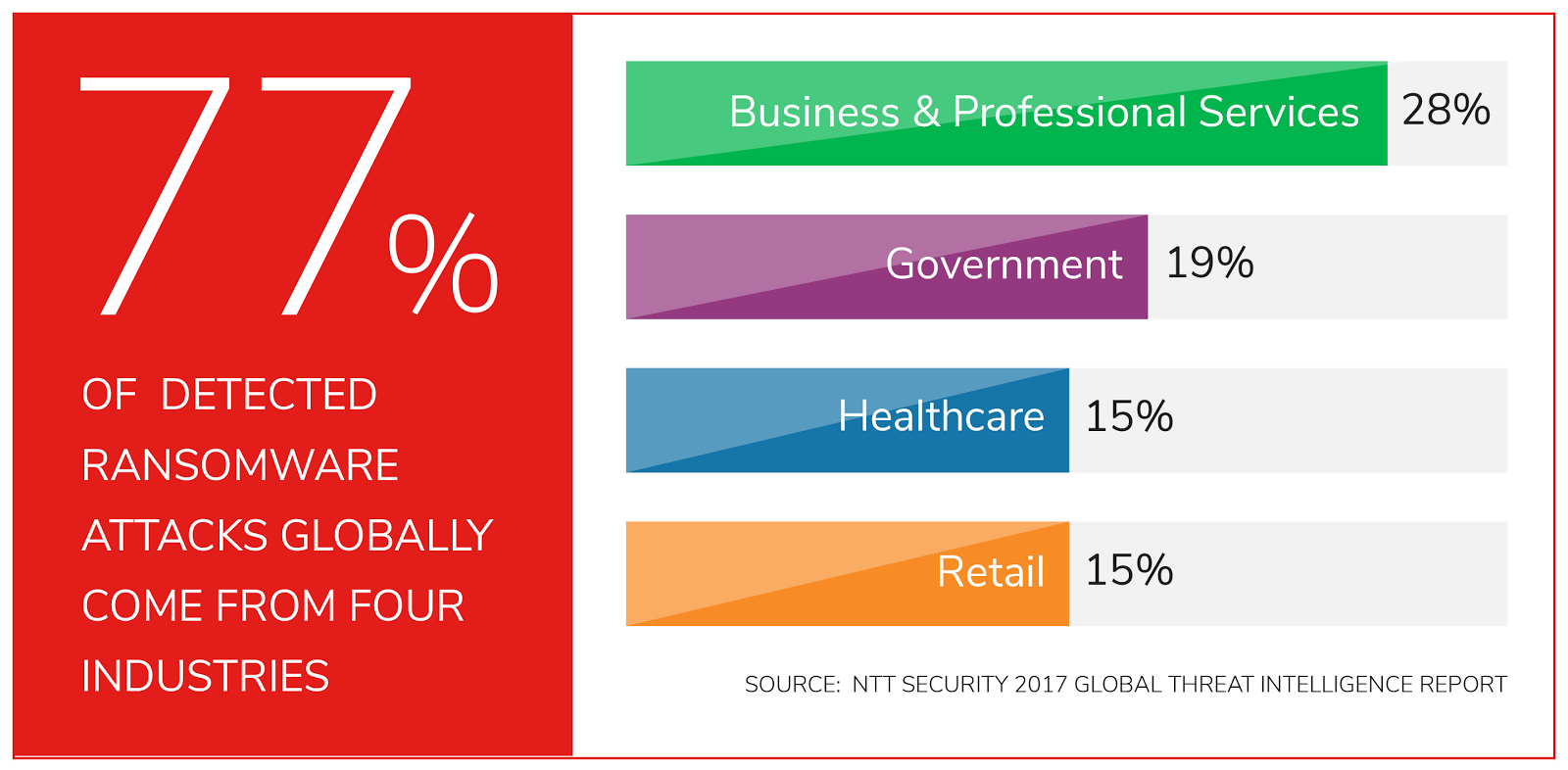
Ransomware, which encrypts data on a victim’s machine and then demands payment of a ransom (usually in bitcoins) to decrypt the data, is running rampant in cyberspace. In fact, ransomware attacks increased more than 600 percent last year compared to 2015. Here’s another frightening statistic: There is a ransomware attack on a company every 40 seconds.
Identity Automation Blog
Blog Categories
- Cybersecurity (134)
- Company News (101)
- K-12 Education (80)
- RapidIdentity (71)
- Multi-Factor Authentication (69)
- Higher Education (44)
- Identity Governance (43)
- Identity Lifecycle Management (32)
- Single Sign-On (32)
- Healthcare (29)
- Access Management (19)
- Government & Public Sector (5)
- Identity Automation Pathfinder (1)
University Security: Implications of BYOD Policies - Part 2
Bring-your-own-device (BYOD) policies are now a necessity for universities and colleges across the country. In Part 1 of this series, we covered the positives and negatives of BYOD, as well as the security implications of such policies. In this post, we’ll go over how to easily implement secure BYOD using a modern identity and access management (IAM) platform.
University Security: Implications of BYOD Policies - Part 1
Bring your own device, or BYOD, is a fast-growing trend on higher-education campuses across the country. In fact, at least 42 percent of U.S. colleges and universities have implemented a BYOD strategy. Meanwhile, bandwidth on campuses has nearly tripled since 2012, with more than 70 percent of schools offering at least 1 GB, in part because of the need to keep up with BYOD demand.
Why Are Flexible Authentication Policies Important in Today's Environment?
Gone are the days of your employees working a standard nine to five from within company walls. Today, employees often work remotely—from different devices and at all hours of the day.
Why You Need to Immediately Cut Data Access When Employees Leave
When your company parts ways with employees, are you able to immediately terminate all access to corporate data? If not, you’re opening the organization up to a very real danger.
Why SMS 2-Step Verification Won’t Keep You Safe
If you’re active with any online service, then you have probably gone through the process of SMS two-step verification, in which a company or app texts a one-time code to your phone as a way to verify you are who you say you are in order to access the service or reset a password. But have you ever stopped to consider how secure this method truly is?
CEOs: Get Everyone on the Same IAM Page
Properly managing cybersecurity risks demands that corporate leadership understands the full potential impact on your business—including reputational and legal risks. This starts with a dialogue about the security risks at your organization—how serious they are, how critical prevention and risk mitigation are, and how sophisticated attackers have become at stealing user credentials and breaching supposedly protected systems.
What Is Risk-Based Authentication?
As businesses onboard more mobile and remote employees, partners, contractors, and other external users, the volume of people needing access to critical systems and data grows exponentially. And while this increased connectivity provides tremendous operational and productivity benefits, it also creates new attack vectors for intruders and cybercriminals.
Identity Management Best Practices: Start with the Basics
Another year, another Verizon Data Breach Investigations Report (DBIR), another depressing look into the state of global cybersecurity preparedness.
Research Shows It Only Takes 9 Minutes Before Stolen Information Is Purchased & Used
What happens when stolen personally identifiable information (PII) is made public? Recently, the Federal Trade Commission (FTC) attempted to answer this question by designing and conducting a study to track the use of stolen information.
current_page_num+2: 9 -