In today’s dynamic business environment, organizations are putting more and more pressure on users to increase productivity without sacrificing security. However, a company’s infrastructure needs to be nimble enough to meet these needs without negatively affecting user experience.
One time passwords (OTPs) are an authentication method commonly used as part of two-factor identification (2FA) and multi-factor authentication (MFA) that can help balance these needs. OTPs are unique passwords that are only valid for a single login session for a defined period of time. Because OTPs aren’t reusable, they overcome many of the shortcomings of traditional (static) passwords by not being vulnerable to replay attacks.
There are several different ways OTPs can be delivered to end users, including soft tokens via a mobile phone app, hard tokens such as key fobs, and on-demand through SMS messages or email. According to a 2017 FIDO Alliance report, 21% of businesses utilize soft tokens, 21% use on-demand, and 16% use hard tokens.
This part of our series will take a closer look at OTP soft tokens.
How OTP Soft Tokens Work
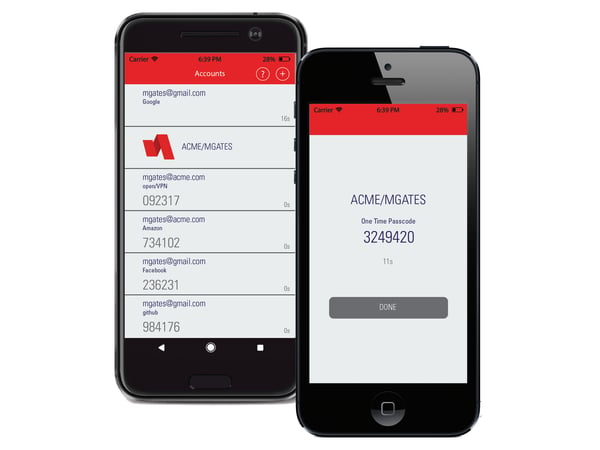
Soft tokens are software programs, typically downloadable mobile authenticator applications, such as RapidIdentity Mobile or Google Authenticator, that effectively turn a user’s device into an OTP generator.
The setup process entails the server generating a secret key. The user enters the secret key into the authenticator application. The user can then generate an OTP to verify the setup process worked with the server.
Each time the authenticator app is opened, a random number is generated for use at a fixed interval. After a specified period of time has elapsed (normally 30 seconds), a new number is presented.
When it is time for a user to authenticate, the user simply enters the current value generated by the mobile authenticator app, along with their username and optionally, a password, PIN, TouchID, or FaceID to log in, effectively adding another layer of security.
Behind the scenes, the server that is authenticating the user runs the algorithm used to generate the OTP. The clocks of the user's device and the server are roughly synchronized, so the numbers entered should match. Once the user’s credentials are validated, the user is permitted to access the service, website, or application.
Benefits
Ease of Use
As most users already have smartphones and are comfortable with mobile technologies, it is easy for them to learn to use soft OTPs and incorporate them into their daily routines. Users tend to keep their smartphones close at hand, making the mobile authenticator application readily accessible.
Works Offline
Because the soft OTPs are generated by a clock-based algorithm that is synchronized across the IT infrastructure, a cell phone signal is not required to authenticate using this method. This comes in handy for situations where a wireless signal isn’t available, such as on flights when airplane mode is used.
Not Vulnerable to Replay Attacks
In addition to offering an extra layer of security, OTPs also mitigate the risk of replay attacks—a shortcoming of traditional passwords. Replay attacks use valid username and password data captured in transmission to fool a system into granting access, effectively replaying the request. Because OTPs are not reusable, even if a would-be intruder were to record an OTP, it would no longer be valid if the intruder tried to use the OTP to log into a service.
Low Cost
Software-based OTPs are a low-cost authentication option because this method can leverage users’ existing mobile devices. This offers significant cost savings versus using hard tokens that must be purchased for each individual user. Additionally, many of the mobile authenticator apps are available as free downloads in mobile app stores.
Ease of Administration
Soft OTPs are easy to manage because most are driven by mobile apps. Users can easily download and install authenticator apps onto their devices by themselves—without IT assistance or having to wait for shipping and delivery of a hard token. This is especially convenient for organizations with remote employees or geographically dispersed locations.
Added Security
Soft OTPs benefit from the added security of the devices upon which the mobile authenticator apps reside. The PIN codes, FaceID, and TouchID integrated into smartphones protect the OTP password generator from unauthorized access in the event that a user’s device falls into the wrong hands.
Furthermore, soft OTPs are more reliable than SMS or email-based OTPs because the information is not being transmitted over the internet or visible on locked screens if the user has notifications turned on.
Drawbacks
Requires a Mobile Device
Soft OTPs require users to complete the login process on their mobile phones. Some users may not want to take this step on their personal phones, and it may not even be an option for users who don't have smartphones.
Additionally, mobile phones have to be charged frequently, and if the battery dies, the user can’t authenticate via this method.
Devices Can Be Lost or Stolen
A soft OTP cannot be used to authenticate if the mobile device itself is lost or stolen. However, in the event this does happen, it’s just a matter of re-provisioning the mobile authenticator app on the user’s new smartphone, unlike with hard tokens, where a new token would have to be purchased and shipped to the user.
Security Vulnerabilities
Soft OTPs are installed on mobile devices, leaving them vulnerable to attacks on the phone’s operating system or other applications. Soft OTPs also utilize a shared secret between the app and the system’s server, each of which can be hacked to access the password.
Furthermore, soft OTPs are still susceptible to man-in-the-middle attacks, whereby an unsuspecting user enters a valid OTP into a phishing site, and the site forwards the user’s current OTP to the official site.
Finally, if individuals use the same mobile phone to access the soft OTP and the service they are authenticating to, both authentication factors are on the same device, contradicting the concept of two-factor authentication.
Are Soft One Time Passwords Right for Your Organization?
Soft OTPs can help organizations meet many of their security and ease-of-use requirements, using existing mobile devices to limit costs, simplify management, and secure data. However, as with any authentication method, there are drawbacks and security vulnerabilities that must be taken into consideration.
If your organization is considering OTPs as a form of authentication, there are multiple methods of delivery to consider. Stay tuned for our upcoming blog posts on OTP hard tokens and on-demand SMS and email OTPs, where we’ll explore the benefits and drawbacks of these methods in depth.

Comments