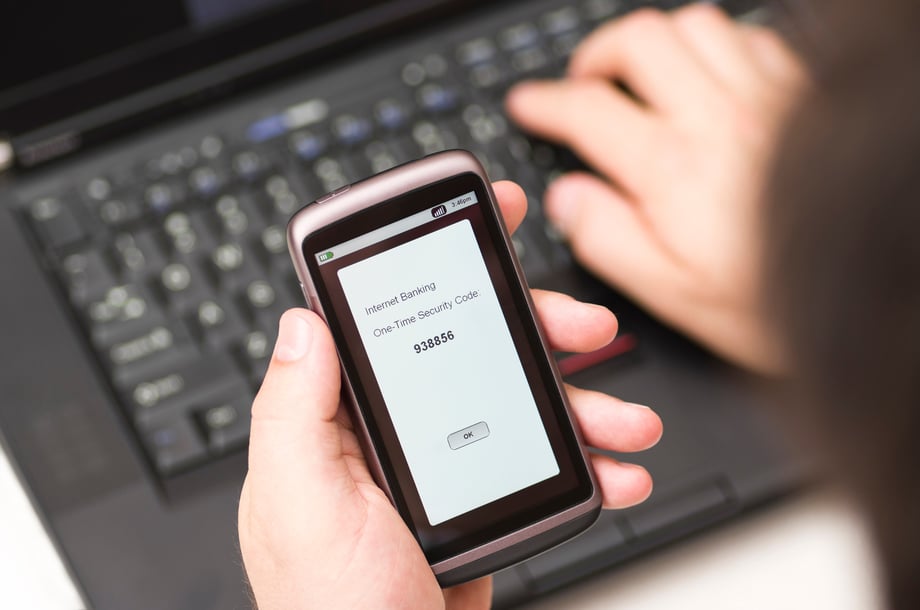
 If you’re active with any online service, then you have probably gone through the process of SMS two-step verification, in which a company or app texts a one-time code to your phone as a way to verify you are who you say you are in order to access the service or reset a password. But have you ever stopped to consider how secure this method truly is?
If you’re active with any online service, then you have probably gone through the process of SMS two-step verification, in which a company or app texts a one-time code to your phone as a way to verify you are who you say you are in order to access the service or reset a password. But have you ever stopped to consider how secure this method truly is?
I was recently in a staff meeting, and my colleague’s phone started buzzing incessantly. She was getting a rapid-fire stream of texts with verification codes for accessing an old payroll system app we no longer use.
Someone had her username and was trying to access her payroll account by resetting her password. We could tell by the number of attempts that it wasn’t a mistake. Luckily, the SMS two-step verification worked as expected. Without the codes being sent to my colleague’s phone, the attacker was unable to login and access the account.
But with so many other authentication methods now available, is SMS really the best option for two-factor authentication (2FA)?
SMS 2FA Basics
Let’s dive a bit deeper into SMS two-factor authentication (2FA). This type of system asks users to first log in with their primary method of authentication, which is usually a username. Next, the system sends an SMS text message to the person with a one time passcode to verify that he or she is the authorized user. The user enters the passcode into the prompt, which in theory verifies his or her identity, and gains access to the application. This system is often used for first-time log-ins or to help a user reset his or her password, as in the example above.
SMS 2FA is popular because it is, above all else, easy. Other than the user’s mobile device, nothing is required. The user doesn’t have to download anything or use a physical hardware reader or physical token—all he or she needs is a phone with the right SIM card.
It is no wonder that SMS has become the default method for two-factor login on web-based apps. At Identity Automation, we even implemented SMS in the past. However, for security reasons, we no longer recommend it. And we’re not the only ones who no longer trust SMS 2FA.
Dismissed By NIST
The U.S. National Institute of Standards and Technology (NIST) announced in July 2016 that organizations should no longer send one time passwords to mobile phones. The reasoning? This approach is simply not secure. NIST—which both corporations and U.S. regulatory agencies look to for cybersecurity compliance—determined that thieves can too easily steal one time passwords sent to phones via SMS text message. (The same applies to voice codes sent over landlines, according to the agency.)
NIST recommends that organizations stop using SMS 2FA and adopt more secure authentication methods.
SMS Vulnerabilities
There’s no doubt that using SMS 2FA is better than relying on passwords alone—a fact my colleague experienced herself when someone tried to access her payroll account. The problem is that attackers are becoming increasingly sophisticated, and SMS 2FA—like most stand-alone authentication methods—is not bulletproof.
Let’s take a look at some of the key SMS 2FA vulnerabilities:
Phones can be stolen.
Of course, any physical device can be stolen—particularly if it’s something people carry around with them all day. And unfortunately, your fingerprint lock is probably less secure than you think, so it won’t necessarily keep the thief from breaking in.
Texts can be viewed without authorization.
Many smartphone users enable text notifications to be visible, so any SMS codes they receive are able to be read without unlocking the phone. Therefore, an attacker could simply take your phone or even just look over your shoulder to steal your authentication code.
SMS codes can be intercepted.
Earlier this year, hackers exploited a vulnerability in Signaling System 7 (SS7), an international telecommunications standard that determines how mobile phones interact, and intercepted text messages before they even made it to the user’s device. Using the intercepted SMS 2FA codes allowed them to access the victim’s bank account.
Meanwhile, apps on a user’s phone can signal another vulnerability. Some, such as Google Messenger and Hangouts, have access to a phone’s SMS inbox. So, if hackers gain access to certain apps, they can also access the user’s texts and remotely steal their 2FA codes.
SMS verification can be spoofed.
A popular phishing technique enables hackers to gain access to people’s email accounts. The attacker only needs to know the victim’s email address and phone number. Then, he or she simply visits the email login page and requests a “reset password” 2FA code be sent to the victim’s phone. Next, the hacker sends the victim an SMS message that says something like, “Suspicious activity has been detected on your account. Respond with the code sent to your phone in order to prevent unauthorized access.” Now, the hacker has the code and can easily gain access to the email account.
Phone accounts can be hijacked.
In an attack called a SIM swap, hackers who know some personal information about their victims, such as the last four digits of their social, call the phone company and have the victim’s phone number moved to an entirely new device. In one case, a hacker used publicly available information to persuade AT&T to reassign the victim’s phone number, then accessed the victim’s PayPal account using SMS 2FA.
SMS 2FA Best Practices
Despite these security vulnerabilities, many organizations opt to stick with SMS 2FA. If your business is still using this approach, it’s important to be careful. At the very least, heighten security by asking your users to follow these best practices:
- Don’t text your two-factor authentication codes to anyone, even if the request appears legitimate.
- Never share or write down your passwords.
- Within apps, never select the option to “remember me” or “save my password.”
- Always use a secure computer with HTTPS Everywhere encryption.
- Change your passwords every few months.
Of course, it’s important to realize that not all users will follow these best practices. Your best bet is to select a more secure authentication method and move away from SMS 2FA altogether.
More Secure Authentication Options
As you consider abandoning SMS 2FA, you might explore the following authentication methods, which are more secure and user-friendly:
Smartphone-Based One Time Password (OTP). An OTP is a password that is only valid for one login session, which means it is less vulnerable to replay attacks than a traditional password. OTPs are created within an app running on a user’s device—rather than sent via SMS message—so they are inherently more secure. However, OTPs are still vulnerable to man-in-the-middle attacks, in which a hacker phishes the user’s OTP.
FIDO U2F. The Fast Identity Online (FIDO) Alliance’s universal second factor (U2F) is an open authentication standard that has become a leading option for 2FA. FIDO U2F uses authenticators, such as mobile phones or USB devices, with secret cryptographic keys, similar to smart cards with public key infrastructure (PKI). The authenticators are usually paired with a username and PIN. Users simply insert their registered U2F token into a USB slot, enter or confirm their username and PIN, then touch the U2F token to prove possession. Since this method doesn’t involve transmitting codes or clear text data, it prevents replay and phishing attacks.
Push Authentication. With Push Authentication, such as RapidIdentity PingMe, a push notification is sent to the user’s registered smartphone for out-of-band authentication that can’t be intercepted at the point of password entry. The user selects “approve” to confirm that he or she initiated the request. Then, the authentication app notifies the target app that the user is confirmed. Push authentication is even faster than typing in a passcode, and it provides a higher level of security, since it addresses the most important SMS shortcomings, such as vulnerability to replay attacks. 
The Ideal Solution: Adaptive Multi-Factor Authentication
While OTP, FIDO U2F, and push authentication are more secure options than SMS 2FA, ideally you would not rely on any one authentication factor. A much better strategy is multi-factor authentication (MFA) that leverages risk-based authentication.
Rather than a one-size-fits-all approach to authentication, in which the same method is used by every user every time, a risk-based approach ensures the optimal level of authentication based on contextual and behavioral factors. The technique uses a risk scoring system to assess the potential risk of every login attempt, and then weighs this score against the allowable risk threshold for a given system. If the risk threshold is triggered, the user must either log in using a stronger form of authentication or answer a series of challenge questions.
For example, let’s say a user logs into her account from the same device, in the same location, every time. If there is no indication that her account may have been compromised, and the systems being accessed are approved for her role, the login can be completed without secondary validation. But if the same user attempts to log in, say, from a different country or on a new WiFi connection, the risk-based authentication solution would recognize the increased risk and generate a second-step verification method that requires the user to be authenticated with a different factor.
Learn More
For organizations looking to evolve beyond SMS 2FA, risk-based authentication provides the ideal balance of security and user-friendliness. For situations, systems, and users with low risk, there is no need for additional authentication. But as risk factors increase, so do authentication requirements. In both cases, the authentication methods are easy to use, providing a frictionless experience in which users don’t even realize they are going through three layers of authentication. As a result, the organization enjoys a higher level of security—without inconveniencing its users.
Learn more about leading 2FA options from Identity Automation.

Comments