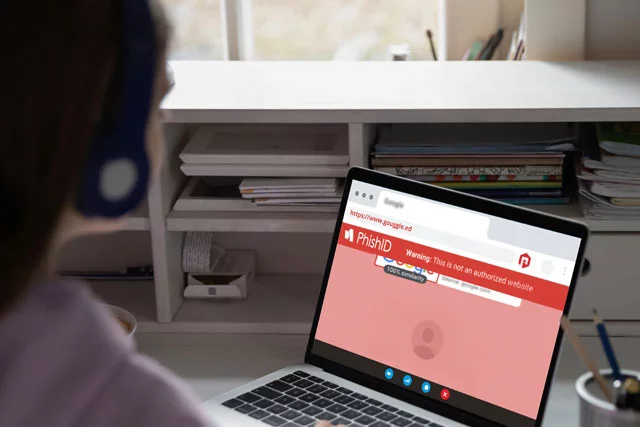
Phishing scammers targeted K-12 schools with fake logins. Learn how the phishing attacks worked and how to keep your school community safe.

Latest Post
Protecting Student Data Before a Vendor Breach Happens
Every IT administrator in education knows the feeling: a breach hits the news, and the first question from every principal, parent and school board member is the same: "Are our students’ data safe?"
Read More