
Recently, we discussed how modern Identity and Access Management (IAM) enables healthcare organizations to reduce risk through security, while also enhancing usability for clinicians. However, there are many, different facets of IAM, spreading across a number of areas and processes in healthcare, and these capabilities are extensive for facilities of all sizes.
Given the span and scope of IAM, it’s critical to create a strong roadmap for advancing the maturity of your IAM framework in order to lower the risk of cybersecurity incidents and make your healthcare organization as efficient as possible. This can be achieved by designing an IAM strategy with thorough up-front planning, successful implementation, and solid operational function.
It’s also important to ensure your IAM platform will have minimal maintenance and can handle reflective policies. So, regardless of what your organization is going through, whether it’s new resources or new processes, the IAM system must have the flexibility to evolve to meet the needs of today and tomorrow.
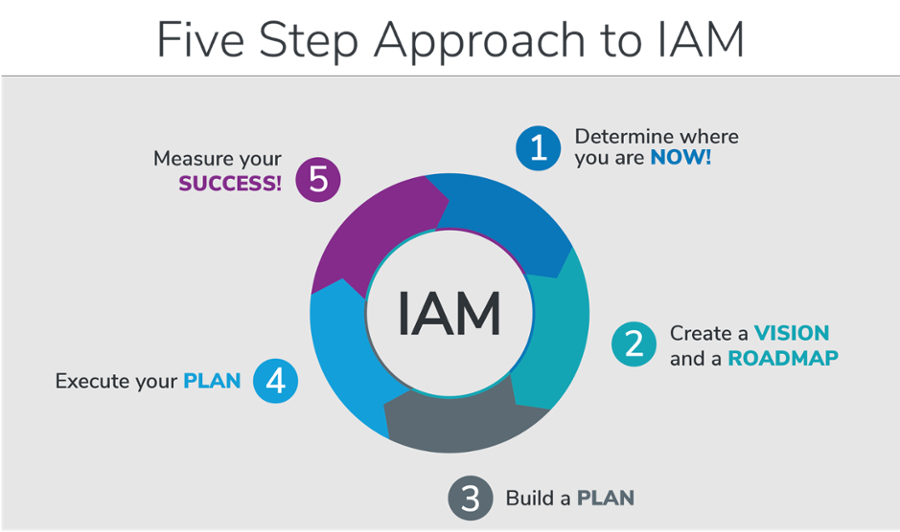
Let’s examine the five actionable steps you can take to establish IAM as a major part of your organization’s cybersecurity initiative and our recommendations to ensure your IAM program runs smoothly.
Approaching IAM in Your Healthcare Organization
Many organizations feel overwhelmed when they are at the early stages of implementing an integrated IAM platform. While they understand the benefits and how IAM addresses the needs of the organization, they often feel there isn’t enough time or resources.
First and foremost, rest assured you don't have to go from 0 to 60 and launch a full IAM program overnight. Rather, we suggest you take a methodical approach and remember planning is key. When you plan the direction you want your organization to go, you can take it in small phases.
To help get you started, we’ve outlined five steps for how to approach IAM in your organization. This model helps healthcare organizations see where they currently stand in terms of their IAM program and plan the next direction to take.
The most important takeaway is to understand IAM is a continuous cycle— a never ending journey. Instead of thinking about your IAM implementation as a project, think of it as a program, just as you would for a cybersecurity program.
Let’s jump into the five steps of an IAM program so you can feel confident that your healthcare organization is secure and set for success.
Step 1: Determine Where You Are Now
First, spend time looking at your processes, data, systems, applications, people, and roles to begin considering where your healthcare organization stands with regard to IAM today. Next, take each tenet of IAM into consideration in terms of where your facility stands and decide what you want to prioritize.
Our recommendation is for organizations to start by increasing Identity Lifecycle Management (ILM) maturity. That’s because ILM is debatably the most important tenet of your entire IAM strategy, as it directly ties into all the applications or services your end users access. So, it helps have ILM implemented first as a foundation for other IAM tenets.
One area many healthcare organizations struggle with providing third-party services, including contractors, vendors, consultants, and more with remote access through firewalls. By placing ILM at the head of the IAM strategy, we can first implement an automated engine that reads from the HR system and allows us to bring in these external identities. Once the automated ILM engine is in place, it’s easier to add other IAM tenets, including Multi-Factor Authentication (MFA) and clinical proximity badge “tap and go”.
Step 2: Create a Vision and a Road Map
The next step is to create a vision of what you want to accomplish and a road map of how you want to accomplish that vision. Step 2 is the planning stage before the execution stage, so it’s critical to know what your strategy should look like.
Establish milestones for measuring the effectiveness of your execution against the plan you created. Make sure you build in checkpoints, check in with key stakeholders, and measure your success with KPIs and applicable data.
Step 3: Build a Plan
In Step 3, you start to get tactical in nature and look at your resources, timing, priorities, financial impact, growth plans, and emerging technology. At this phase, you build the steps on your roadmap to get to where you want to go. This is also where the milestones are incorporated, so that during the execution phase, you can determine if the level of progress is appropriate, or if adjustments are necessary.
We also recommend conducting research at Step 3 to ask yourself and your team questions such as: What parts do I have to move around first to get to where I need to go? What investment is going to be needed, if any? What am I going to have to do in terms of priority to make sure I can focus on executing this plan?
Step 4: Execute Your Plan
Step 4 is the execution of the tactical steps for each planned phase of your IAM program. For example, if you're introducing ILM and your plan is to implement an engine that can take information from your HR system, this step would be the actual execution.
Furthermore, at Step 4 you should consider the level of integration or how seamlessly the new system or technology ties in with your other systems. Certain tactical steps of your IAM program will have dependencies that must be completed before increasing maturity, or will serve as dependencies for future phases. Executing and measuring against your plan is critical to moving your IAM program forward appropriately and efficiently.
Step 5: Measure Your Success
Step 5 step addresses the question: Did you achieve what you set out to do? At this step, determine if you ultimately reached the level of IAM maturity you planned for this phase of your program. If you run into an issue, take a step back, course correct, make an adjustment, and continue on.
Once you’ve achieved your vision and measured your success, identify the next priority or desired level of IAM maturity your organization aims to achieve. Consider what capabilities you need to meet your priorities and what is realistic based on your resources.
IAM itself is a journey and a program, it should never go away, and it does not have a destination, except to continue improving. That’s why this model is cyclical and doesn't stop. Once the first phase is completed, you move onto the next desired level of IAM maturity and start the process again at Step 1.
As you approach each phase or cycle, treat it as a project inside your IAM program. Remember to first create your vision of what you want to accomplish and next design the roadmap, or how you will execute, so that you can achieve the vision you set out to do.
Kickoff Step 1 Today with Our Maturity Assessment Tool
Delivering healthcare in 2020 is much different than it was five to ten years ago. The security perimeter has changed over the years and will continue to evolve. So, as new technologies emerge and we transform our digital technology, we have to continue to move the goal line of our vision. While you’ll have projects within your IAM program, don't stop or reach a conclusion, rather, you must continue to enhance.
As getting started can be the hardest part, we’ve created a couple of resources to help you along the way. First, our Identity and Access Management Capability Maturity Model outlines the seven tenets of IAM to provide a background understanding of IAM capabilities and what capabilities are achievable today.
Next, our Maturity Assessment Tool provides an overall IAM maturity score for your healthcare organization and also equips you with a score in each tenet, along with actionable steps for increasing maturity. This tool helps organizations to identify their security and usability gaps, set benchmarks, and establish priorities.
Start with Step 1 today and evaluate your healthcare organization with the Maturity Assessment Tool here.


Comments