While the country as a whole has had more than seven years of recovery time since the Great Recession, many government agencies and institutions still find themselves struggling to fully mend. Across the U.S., many are still working to do more with less—a reality that is particularly true in public colleges and universities.
Identity Automation Blog
Recent Posts by Kathleen Garska
Enterprise Password Management: Mandatory Changes Out and MFA In
In enterprises around the globe, it’s becoming increasingly clear that implementing mandatory password changes is no longer considered best practice for securing key systems and data.
Of course, we’ve long known that passwords are a weak link in the security chain. Eighty percent of hacking-related breaches in 2017 leveraged either stolen passwords and/or weak or guessable passwords, according to the latest Verizon Data Breach Investigations Report.
Identity Management Best Practices: Start with the Basics
Another year, another Verizon Data Breach Investigations Report (DBIR), another depressing look into the state of global cybersecurity preparedness.
Research Shows It Only Takes 9 Minutes Before Stolen Information Is Purchased & Used
What happens when stolen personally identifiable information (PII) is made public? Recently, the Federal Trade Commission (FTC) attempted to answer this question by designing and conducting a study to track the use of stolen information.
5 Reasons Not to DIY Identity and Access Management
At colleges and universities across the country, a hidden danger is lurking. It may have once seemed innocent, but in today’s world, it is a legitimate threat: Custom identity and access management (IAM) solutions cobbled together with custom scripts.
Research Shows It's High Time for MFA in Higher Ed
A recent report, Cyber Criminals, College Credentials, and the Dark Web from Digital Citizens Alliance (DCA), confirms what has long been feared: The problem of hackers stealing the usernames, passwords, and personal information of students and faculty from colleges and universities and selling this information on the dark web is greater than most realized.
Why You Must Consider IAM Before Your Cloud Migration
With an incredible 95 percent of organizations already using the cloud in some fashion, it’s no surprise that there is an endless stream of advice on how to achieve a successful cloud migration.
Why Most Identity Management Software Can’t Handle Transient Users at Scale
While every business faces some level of transience in its operations—namely employee or customer churn—community colleges, by the nature of their business, face the issue on a massive scale. For example, At Lone Star College, the nation’s third-largest higher-education system, up to 40 percent of the schools’ 100,000 students are transient users.
Yes, You Should Be Concerned about Rogue Employees (and Here's Why)
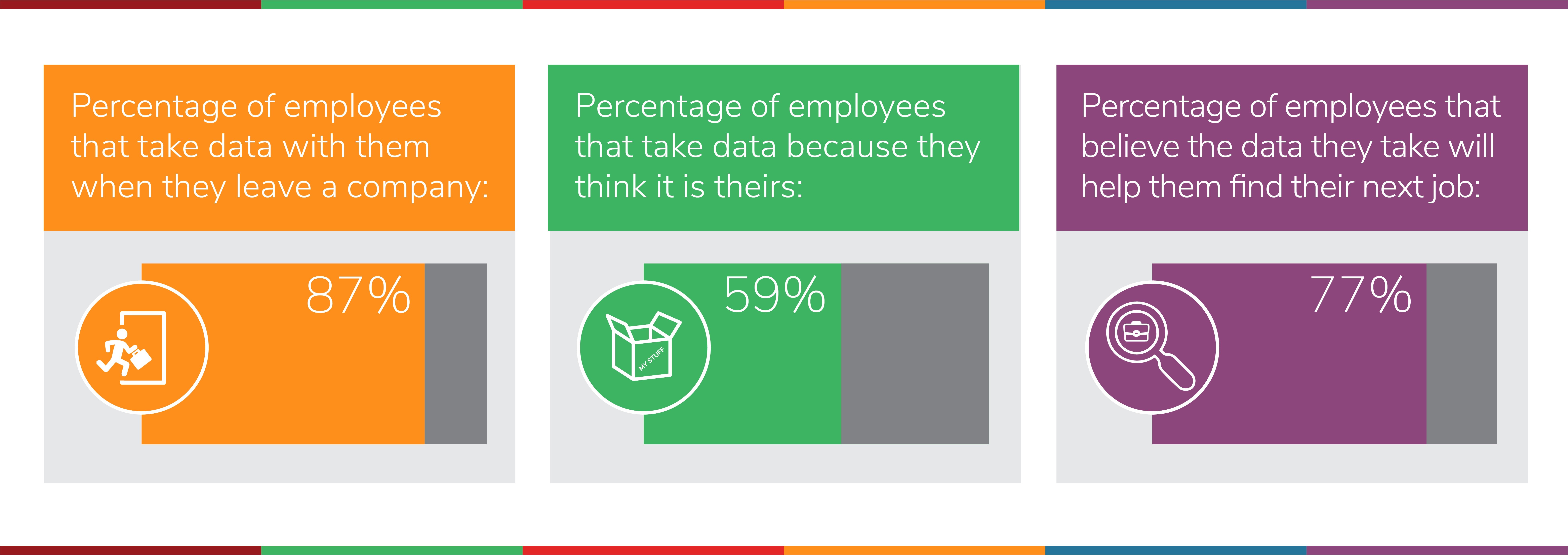
In IT security, it’s often said that a company’s employees are its weakest link. As technology grows increasingly user-friendly, and the rules of digital “ownership” blur, rogue employees—those who don’t follow the standard IT security rules for one reason or another—are emerging as a significant threat to corporate security.
Our Thoughts on InformationWeek’s “Five Ways to Shine a Light on Shadow IT”
The term shadow IT conjures up images of a malevolent, invisible force that poses a threat to security policies. Sounds scary, right? While shadow IT does have the ability to create a bottleneck, it tends to occur in the most benign of situations.
current_page_num+2: 11 -