Healthcare mergers and acquisitions (M&As) are happening more frequently than ever. In fact, 2017 was a banner year for M&As, with 115 transactions, including 10 deals between hospitals with a net revenue of over $1 billion—the highest number in recent history.
Identity Automation Blog
Blog Categories
- Cybersecurity (134)
- Company News (101)
- K-12 Education (80)
- RapidIdentity (71)
- Multi-Factor Authentication (69)
- Higher Education (44)
- Identity Governance (43)
- Identity Lifecycle Management (32)
- Single Sign-On (32)
- Healthcare (29)
- Access Management (19)
- Government & Public Sector (5)
- Identity Automation Pathfinder (1)
Recent Posts by Kathleen Garska
Choosing the Right Proximity Badge Access Solution for Your Healthcare Organization
In busy hospital settings, clinicians move from room to room and department to department. They require multiple logins as they switch from one workstation to another and access multiple endpoint devices, such as thick and thin clients running Windows- or Linux-based operating systems.
Why Legacy, Homegrown, and Open-Source IAM Systems Can't Address Higher Education's Identity Management Challenges
While higher education institutions face many of the same identity and access management (IAM) challenges as corporations, they also must overcome a number of complex and unique hurdles that typically aren’t seen in corporate enterprise deployments.
Security Breaches in Healthcare That Scare Even Us
Though many of us know that healthcare data is valuable, not all of us are aware of exactly how valuable it is. Electronic health records (EHRs) are a one-stop shop for all the data a hacker wants: medical, financial, and personal. Some data doesn’t age either—for example, your birth date and Social Security number never change.
Two-Factor Authentication (2FA) Explained: Email and SMS OTPs
One time passwords (OTPs) are a popular choice for organizations looking to step up their security with two-factor authentication (2FA). These randomly generated passwords are only valid for a single login session and overcome many of the vulnerabilities of traditional passwords.
Two-Factor Authentication (2FA) Explained: Challenge Response Authentication
Challenge/Response, also known as knowledge-based authentication, is a form of authentication where users verify their identities by answering “challenge” questions based on personal information about the user.
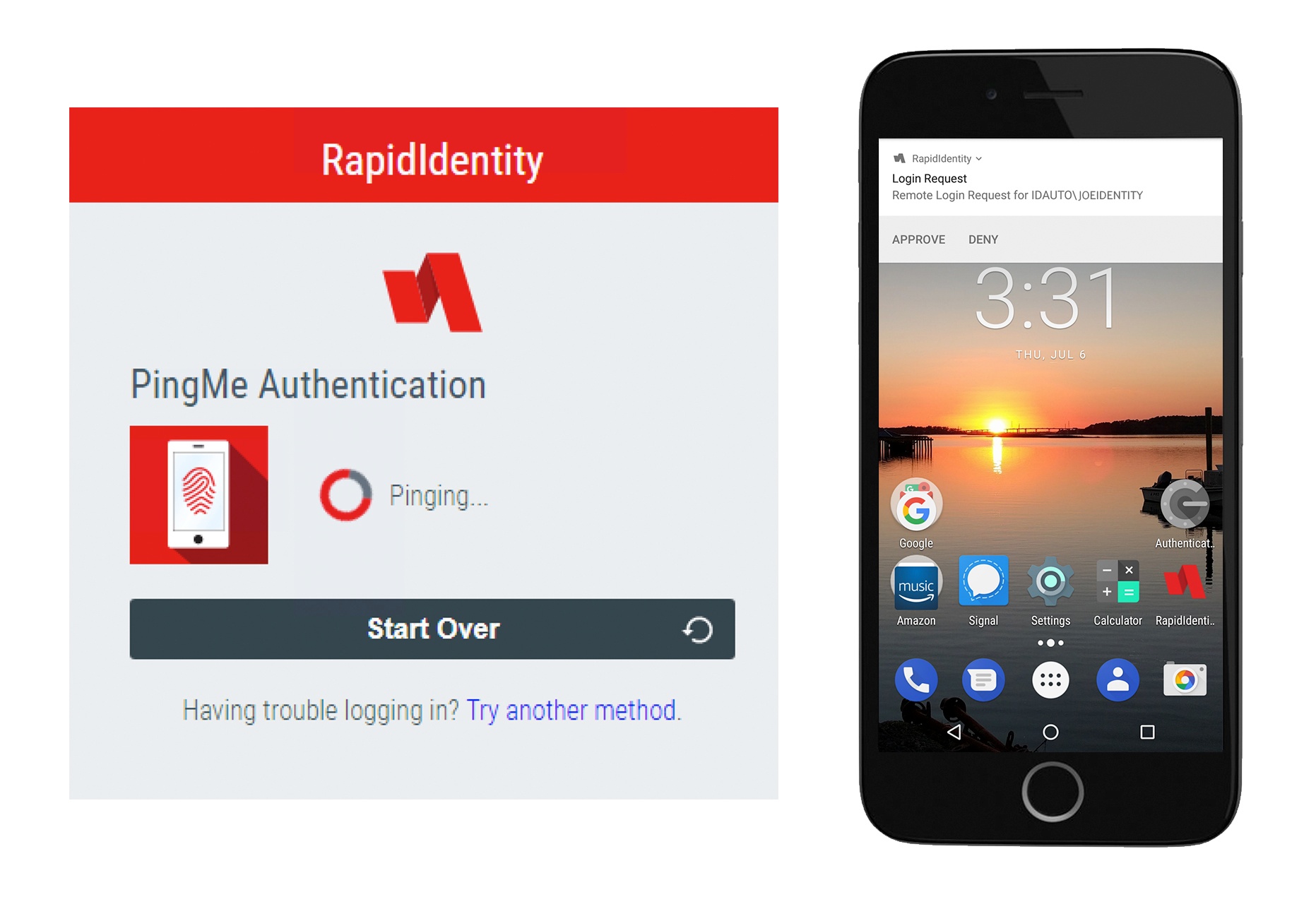
Two-Factor Authentication (2FA) Explained: Push Notifications
More and more, organizations are looking for cost-effective alternatives to traditional passwords that increase security without affecting usability. Many people believe that push notification authentication, a newer mobile-based authentication method, could be the answer.
Two-Factor Authentication (2FA) Explained: RFID Access Control
Historically, magnetic stripe cards were used for access control. However, these cards aren’t particularly secure, as the information stored on them is typically not encrypted. Additionally, they have to be physically swiped, leading to issues with wear and tear.
Two-Factor Authentication (2FA) Explained: 2D Barcode Authentication
As part of our 2FA Explained series, we recently looked at magnetic stripe cards. Another authentication method that has long been in use and can be printed onto cards are 2D barcodes.
Onboarding and Offboarding: 7 Identity Lifecycle Management Challenges Solved with Modern IAM, Part 2
In Part 1 of this series, we discussed the challenges that come with onboarding employees and granting access, specifically determining which permissions to give an employee, providing employees with day one access, and managing ad-hoc access requests.
current_page_num+2: 4 -